In the near future, we may reach a turning point for humanity, a moment that those in cybersecurity circles ominously label “Q-Day.” This refers to the day a quantum computer is created that possesses the capabilities to crack widely used encryption, rendering our most intimate digital secrets open to anyone with bad intentions. Consider the implications: our emails, text messages, monetary transactions, health records, and even critical infrastructure data could become vulnerable overnight. As Michele Mosca highlights, we are effectively playing a perilous game of Russian roulette with our data and, by extension, our privacy and security.
Several projections paint a concerning picture that suggests there could be a one-in-three chance of encountering Q-Day by 2035. Alarmingly, some experts speculate that this day may have already arrived, implying that dangerous technology might be in the hands of malicious actors right now. It’s a horrifying possibility that evokes a sense of urgency: how do we safeguard ourselves when we may be standing on the precipice of an era where our digital lives are exposed?
The Quantum Arms Race
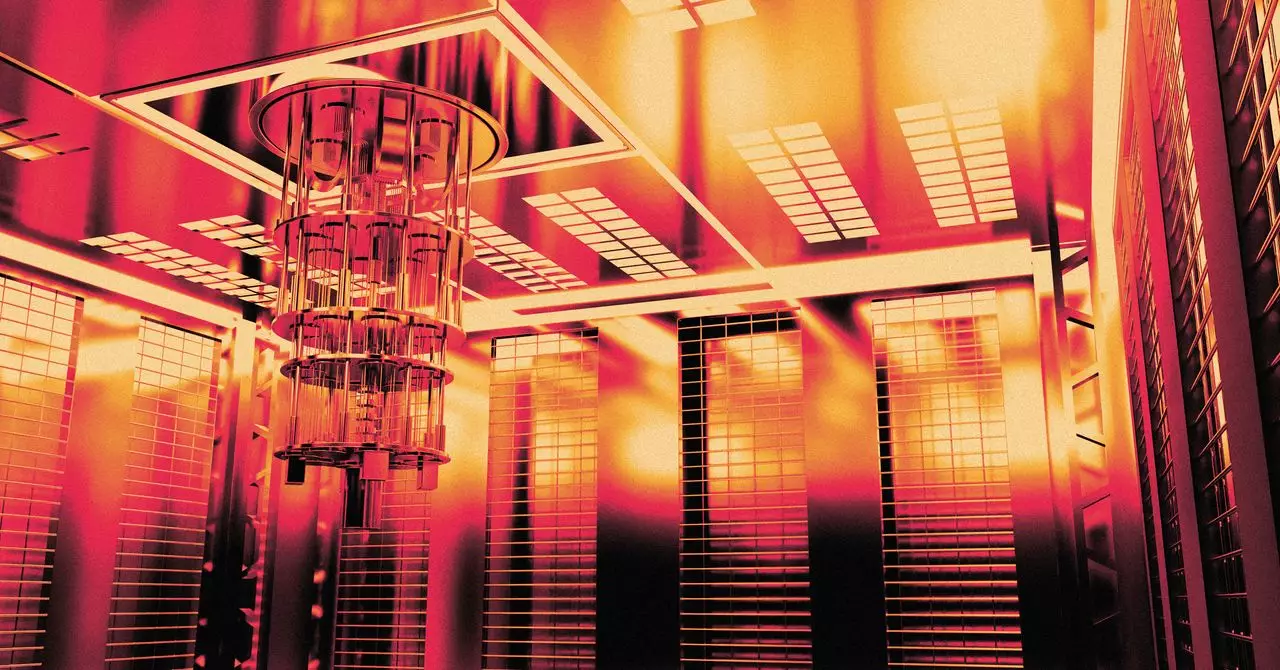
While the corporate AI race has captivated public attention with its advancements in machine learning and automation, an equally compelling struggle is underway in the realm of quantum technology. This emerging field, leveraging the strange and counterintuitive behaviors of subatomic particles, represents a paradigm shift in computing. Unlike classical computers, which are bound strictly by binary (0s and 1s), quantum computers can inhabit multiple states at once. This unique ability allows them to tackle complex problems in ways we have previously only dreamed of, particularly in encryption.
Tech giants—including Google, Huawei, IBM, and Microsoft—have mobilized substantial financial and intellectual resources towards unlocking quantum potential. Their pursuits span far beyond merely developing quantum systems; they aim to grasp advanced capabilities in materials science, drug discovery, and market analysis. Meanwhile, nations such as China are investing heavily, led by a state-backed agenda to position themselves at the forefront of this technological race. The stakes are extraordinarily high, as whoever emerges victorious will not only possess groundbreaking capabilities but will also hold the key to history’s most formidable code-breaking apparatus.
The Consequences of a Quantum Breakthrough
What kind of world awaits us on Q-Day? One potential scenario is a gradual erasure of privacy, marked by a series of seemingly unrelated events that would lead people to eventually realize that their lives have been intruded upon. For instance, critical infrastructure failures, such as the collapse of a city’s energy grid or the leaking of confidential governmental communications, may be the first signs of a quantum-enhanced cyber breach.
Alternatively, the realization could strike in a much more chaotic fashion—an apocalyptic breakdown where every sector of society feels the impact simultaneously. Imagine an orchestrated attack that brings down the power grid, disrupts modern transportation systems, and hacks into financial institutions across the globe. The sheer scale of such an event could redefine reality as we know it, leading to societal upheaval.
In this volatile environment, individuals would have to contend with the harsh reality that their private lives are no longer private, leaving the line between public and personal nearly indistinguishable. The ability to manipulate or expose secrets could reach unprecedented heights, creating fertile ground for exploitation, blackmail, and societal discord.
Preparing for the Inevitable
Given the alarming predictions surrounding Q-Day, the pressing question remains: What measures can we take to mitigate the potential disastrous outcomes? As quantum technology evolves, so too must our approaches to cybersecurity. Developers and organizations need to prioritize creating quantum-resistant encryption methods that can withstand the scrutiny of powerful quantum machines.
Furthermore, heightened awareness and education surrounding these emerging technologies are essential—society must be informed about the potential risks and take proactive steps to protect personal data. Individuals should also reflect on their online habits, understanding that when quantum computers become a reality, the digital footprint we leave may leave us exposed in unimaginable ways.
With the countdown to Q-Day in motion, the battle between quantum innovation and cybersecurity is not just a technological challenge—it embodies a broader societal issue that demands urgent attention. In a society striving for connectivity and openness, how we navigate this landscape in the coming years will fundamentally shape our collective future.